A bug in the Android mobile operating system has been discovered by researchers, who say it affects nearly a billion devices.

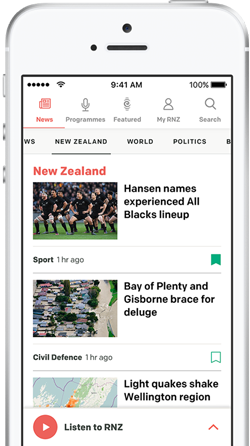
Photo: AFP
The flaw can be exploited by sending a photo or video message to a person's smartphone, without any action by the receiver.
Google said it had patched the problem, but millions of devices still need their software updating.
The researchers said the flaw was "extremely dangerous".
Researchers from US information security company Zimpherium said they believed it was one of the worst Android vulnerabilities to date, estimating that 950 million devices were affected.
Hackers were able to send malicious code within a multimedia message that could access a service within Android called Stagefright.
After Stagefright had been invoked, which required no action from the victim, other data and apps on the handset could be accessed by the malicious code.
"These vulnerabilities are extremely dangerous because they do not require that the victim take any action to be exploited," the researchers wrote.
Further details on the flaw will be revealed by the team, at the Black Hat security conference in Las Vegas next week.
James Lyne, global head of security research at security company Sophos, said the flaw affected a "massive array" of phones running Android version 2.2 and higher.
"On some devices, the privileges at which this runs means an attacker could access all kinds of content on your device or access resources such as the camera," he said.
Rush to patch
Zimpherium's researchers notified Google, which subsequently produced a patch to fix the problem.
However, millions of devices currently remain unpatched because hardware manufacturers and mobile operators have to distribute updates to customers themselves, and customers can reject updates manually.
In a statement, Google said: "This vulnerability was identified in a laboratory setting on older Android devices, and as far as we know, no-one has been affected.
"As part of a regularly scheduled security update, we plan to push further safeguards to Nexus devices starting next week.
"And, we'll be releasing it in open source when the details are made public by the researcher at Black Hat."
-BBC